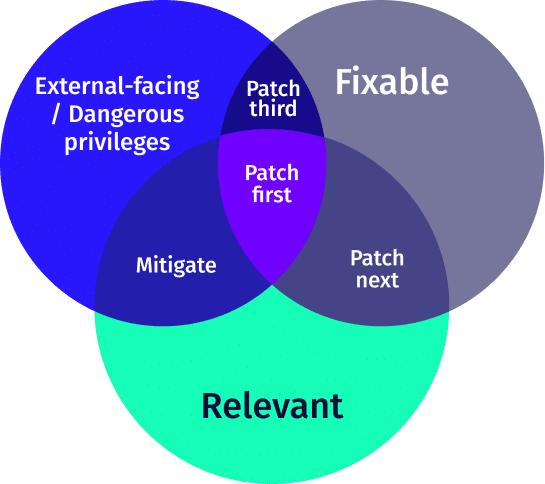
What is CVE Relevancy?
The term “CVE shock” refers to the overwhelming sensation felt by DevOps and security teams when confronted with an overwhelming number of vulnerabilities. The sheer quantity of vulnerabilities can make it difficult to determine which ones are the most critical and should be addressed first. However, CVE relevancy offers a solution to CVE shock by guiding teams towards the vulnerabilities that pose the greatest risk to their operating clusters. By focusing on these high-priority vulnerabilities, teams can effectively prioritize vulnerabilities, so they can get on with task of patching, making an actual impact on security.
CVE Prioritization options
To date, the common best practice for solving vulnerabilities is according to their score, as it is defined under the Common Vulnerability Scoring System.
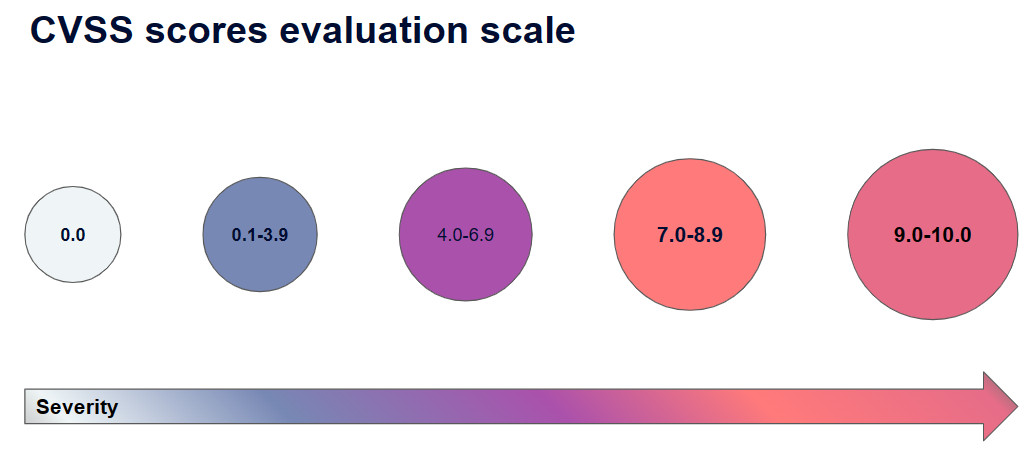
Which means teams will work their way down from the vulnerabilities with the highest score to the lowest. The problem with this approach is twofold. Firstly, it perpetuates the problem of “CVE shock”. The second and more important problem is that working this way doesn’t necessarily make an impact on your cloud security posture.