What is cloud compliance?
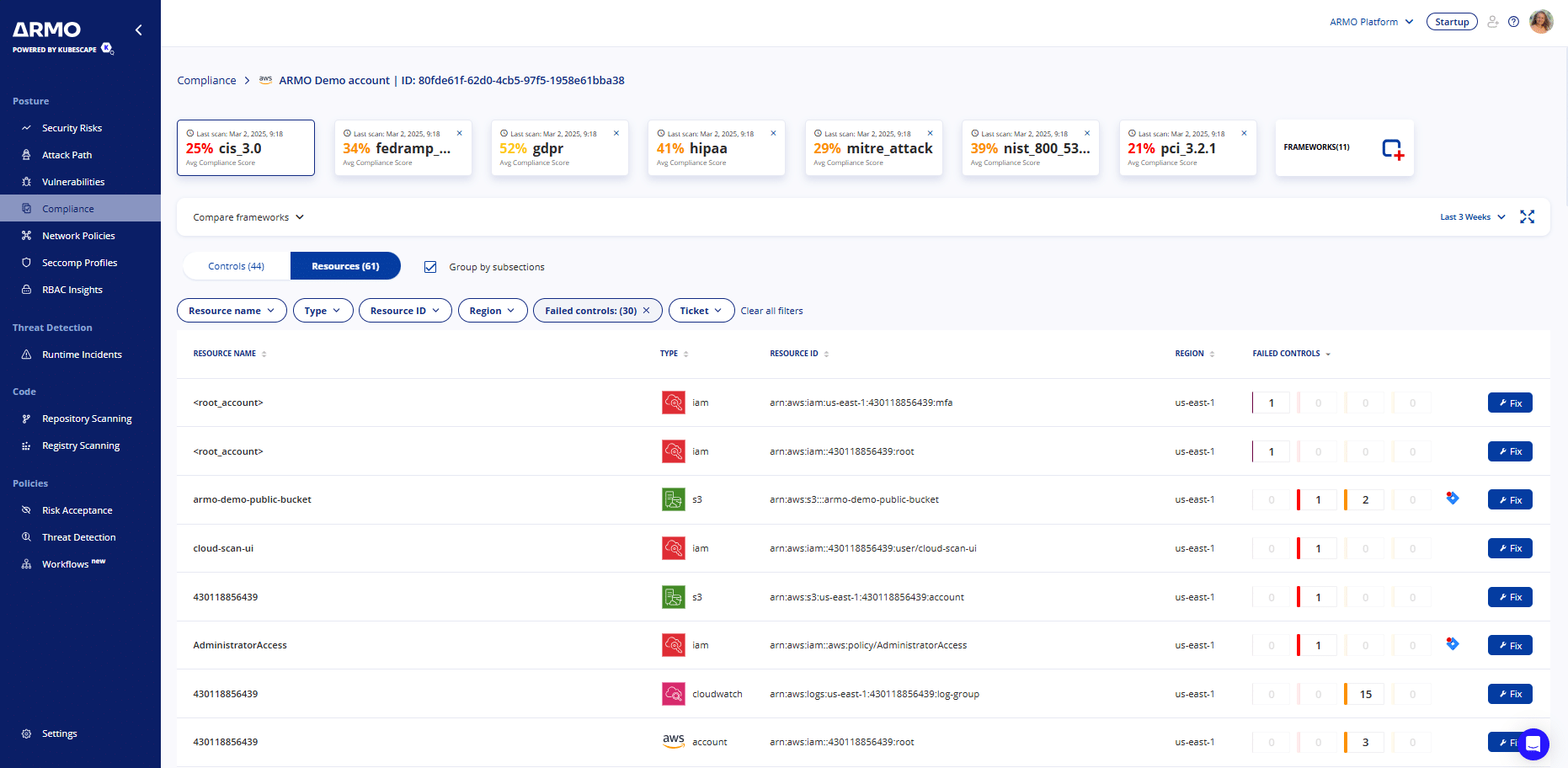
Cloud compliance encompasses various aspects of the platform, including security, data privacy, network security, and incident response. The aim of making your cloud infratsructure compliant is to minimize the risk of security breaches and protect sensitive data.
Why care about cloud compliance?
Cloud infrastructure compliance ensures adherence to industry standards and regulations, where applicable. It also helps with ensuring the smooth operation of the cloud infrastructure. Adopting cloud native technologies presents new compliance challenges, due to the dynamic nature of cloud workloads. Yet, if you’re a service organization that stores, processes, or transmits any kind of customer data, you’ll likely need to be compliant. Not to mention that a single data breach can cost millions, in addition to the reputation hit and loss of customer trust