Kubernetes Runtime Security
Kubernetes is a complex system, and operators often overlook runtime security even though it’s crucial to managing a Kubernetes implementation. With all the native tools available to manage privileges and secure workloads, it’s natural for devsecopsteams to focus on Kubernetes posture and clustersecurity and forget about runtime protection. Organizations must secure their Kubernetes implementations and workloads in production against threats with sophisticated attacks on the rise.
What is Kubernetes Runtime Security?
Kubernetes runtime security aims to protect containers and workloads against threats while the containers are running in production. What distinguishes it from overall Kubernetes security is that it’s focused on protecting workloads from threats that only emerge against deployed containers. Runtime threats occur in real-time in production, making them challenging to assess and prevent. Compromised containers can create a significant security breach because there is potential to impact other processes.
Kubernetes Runtime Security Threats
In an ideal scenario, operators prevent runtime threats from compromising live environments with robust access controls and workload isolation. Unfortunately, there are still some runtime threats that commonly emerge in deployed containers:
- Attackers can exploit vulnerabilities to deploy unauthorized containers
- Misconfigured containers provide unauthorized access to sensitive information.
- Malware can be hidden and activated inside a container image.
- Privilege escalation attacks can lead to exploiting container runtime vulnerabilities.
To nail down these threats, it’s essential to leverage enforcement tools and techniques to properly configure access controls to prevent unauthorized access to resources and secrets. Even when outright prevention is impossible, using the right tools and methods can mitigate the worst impacts and isolate issues within a single container.
Best Practices for Kubernetes Runtime Security
Operators can reduce the attack surface of Kubernetes implementations in runtime by applying sound security practices in production. Here are a few actions that all security teams should take in managing against runtime security threats:
- Although this is something done before deployment typically, operators must continuously scan images for misconfigurations and vulnerabilities to ensure malware won’t exploit it in a production environment. Maintaining security in Kubernetes requires continuous rigor throughout the lifecycle, and it begins with risk compliance and image scanning.
- Given that access control policies are a critical vulnerability in Kubernetes implementations, it’s essential to routinely scan for policy anomalies in RBAC Files and deployment files. These scans can detect RBAC policies violations and prevent or mitigate runtime breaches.
- Kubernetes secrets are the native sources for storing and managing sensitive data in Kubernetes. While Kubernetes offers some protection natively, there are still some open risks that organizations should consider outside tooling to resolve.
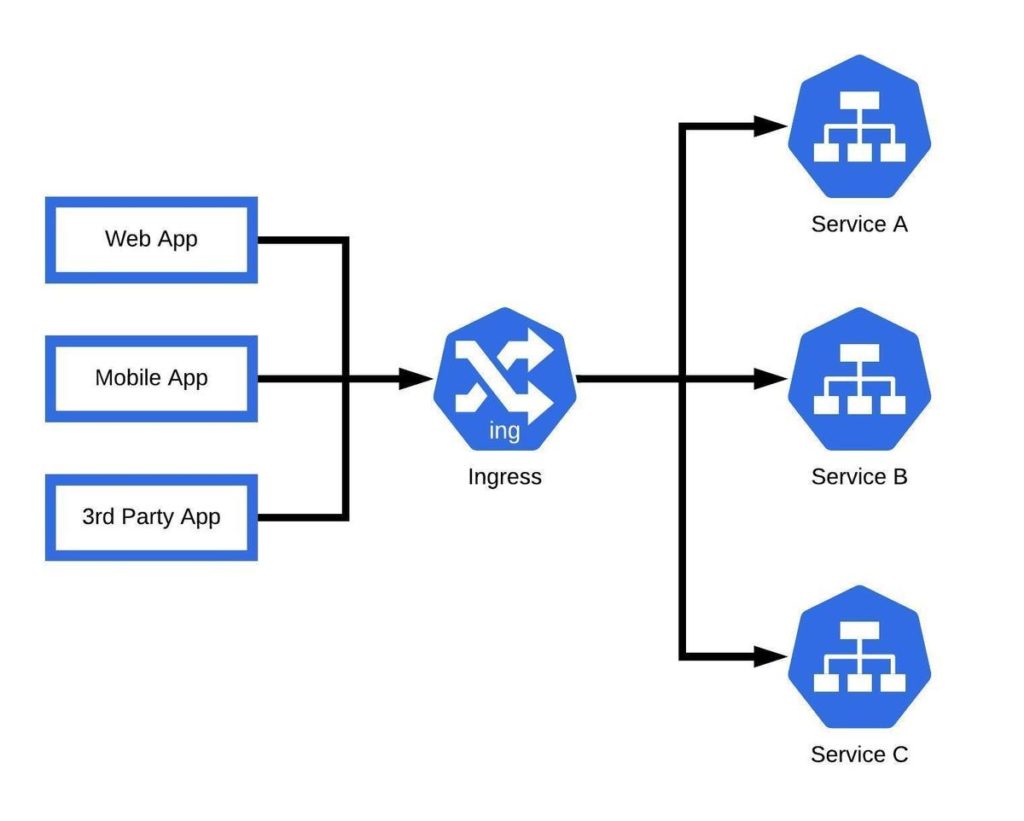
- Service mesh technology facilitates the separation of networking and business logic. Because of the complex nature of these products and the infrastructure they help to manage, its important to leverage automation as much as possible. In addition, developers should minimize redundant clusters as much as possible, which helps greatly reduces the complexity of operating service mesh.
- It’s impossible to detect anomalies without a clear understanding of expected behavior. Developers and operators should establish a clean baseline to assess threats against typical behavior. That will improve outcomes related to tools and techniques designed to detect and mitigate anomalies in runtime environments.
- Sometimes Breaches happen. When they do, the most crucial factor in mitigation is containment—Monitor network traffic between containers and pods to detect threats spreading across multiple processes. Leverage zero-trust policies wherever possible.
- Microsegmentation can greatly improve the security posture of Kubernetes implementations by creating a trust boundary around every single workload in the cluster.
Runtime Security is the last line of protection
Once a threat emerges in runtime, it means that all of an organization’s protections in pre-production have failed. That makes it more critical to continuously audit, scan, and secure runtime environments against breaches. Even when operators can’t entirely prevent a threat, a rigorous approach to runtime security can mitigate damage and help contain threats to isolated workloads and environments. To learn more, watch a demo.