Seccomp
What is Seccomp?
Seccomp is a robust tool that strengthens the security posture of Linux-based environments. Explore how leveraging seccomp can add an extra layer of defense to your Docker containers and Kubernetes clusters.
Understanding Seccomp and its role
Secure Computing Mode (seccomp), a crucial Linux kernel component empowers administrators and developers to restrict the system calls available to a process. It provides a secure, controlled environment for applications, limiting their interaction with the kernel to only authorized system calls. By doing so, seccomp significantly reduces the attack surface of containers and pods, making it an invaluable asset for Kubernetes security.
Seccomp functions as a system call filter, acting as a gatekeeper between applications and the kernel. It executes this role by scrutinizing each system call made by an application and permitting only authorized calls to pass through. This meticulous filtering process is instrumental in reducing the attack surface and mitigating potential security threats.
Two key security strategies are default seccomp profiles and seccomp filters. Default profiles provide foundational safety by limiting system calls. Seccomp filters offer precise, customizable security configurations.
Default Seccomp Profiles: One of the first steps in leveraging seccomp for enhanced security is to utilize default seccomp profiles. These profiles are pre-defined sets of allowed system calls for a container or process. By employing default profiles, you can ensure that only essential and safe system calls are permitted, mitigating the risk of malicious exploitation.
Seccomp Filters: For more advanced and tailored security configurations, seccomp filters come into play. Seccomp filters allow you to specify precisely which system calls should be allowed or denied for a given container or process. This fine-grained control empowers you to adapt seccomp to your application’s needs, minimizing potential reducing security risks.
Building blocks of security: understanding Seccomp components
Seccomp comprises several critical components, including Berkeley Packet Filters (eBPF), system call tables, and filtering modes. These components work in tandem to define and enforce security policies.
- Berkeley Packet Filters (eBPF): They allow you to define complex rules and conditions for filtering system calls. eBPF provide flexibility in specifying which system calls are allowed, denied, or subject to additional scrutiny.
- System Call Tables: Seccomp relies on system call tables to determine which system calls are available and can be controlled. These tables contain information about the kernel-supported system calls, and seccomp policies reference these tables to enforce restrictions.
- Seccomp Modes: Seccomp operates in two primary modes: ‘strict’ and ‘filter.’
- Strict Mode: A minimal set of essential syscalls is allowed in’ strict’ mode. This mode is highly restrictive and suitable for scenarios requiring the absolute minimum of system calls.
- Filter Mode: ‘Filter’ mode allows you to define custom policies specifying which syscalls are permitted and which are denied. This mode offers greater flexibility for tailoring policies to specific use cases.
- Seccomp eBPF Programs: These are user-defined programs that contain filtering rules for system calls. These programs are written in eBPF assembly language or, more commonly, in a higher-level language like C. They are loaded into the kernel and enforce the seccomp policy by evaluating system calls against the defined rules.
- Action Rules: Within seccomp eBPF programs, you can define action rules for each syscall. These rules specify the action to be taken when a particular syscall is encountered. Actions can include allowing the syscall, denying it, logging it, or generating an error.
- Return Values: Seccomp eBPF programs can also specify return values for syscalls. Return values dictate what the syscall will return to the calling process. This can be useful for fine-tuning the behavior of a process based on the outcome of a syscall.
- Error Handling: Seccomp policies can include error handling mechanisms to deal with unauthorized or denied syscalls. These mechanisms ensure that the process is terminated when a syscall is denied or the appropriate error code is generated.
- Permitted and Denied Syscalls: One of the core functions of seccomp is to specify which syscalls are permitted and which are denied. This is the heart of the security policy, as it defines what actions processes can or cannot perform.
Understanding these key components of seccomp is essential. It helps you craft effective security policies and leverage seccomp to enhance the security of your Linux-based systems, particularly within containerized environments like Kubernetes.
Integrating Seccomp with Docker containers and Kubernetes
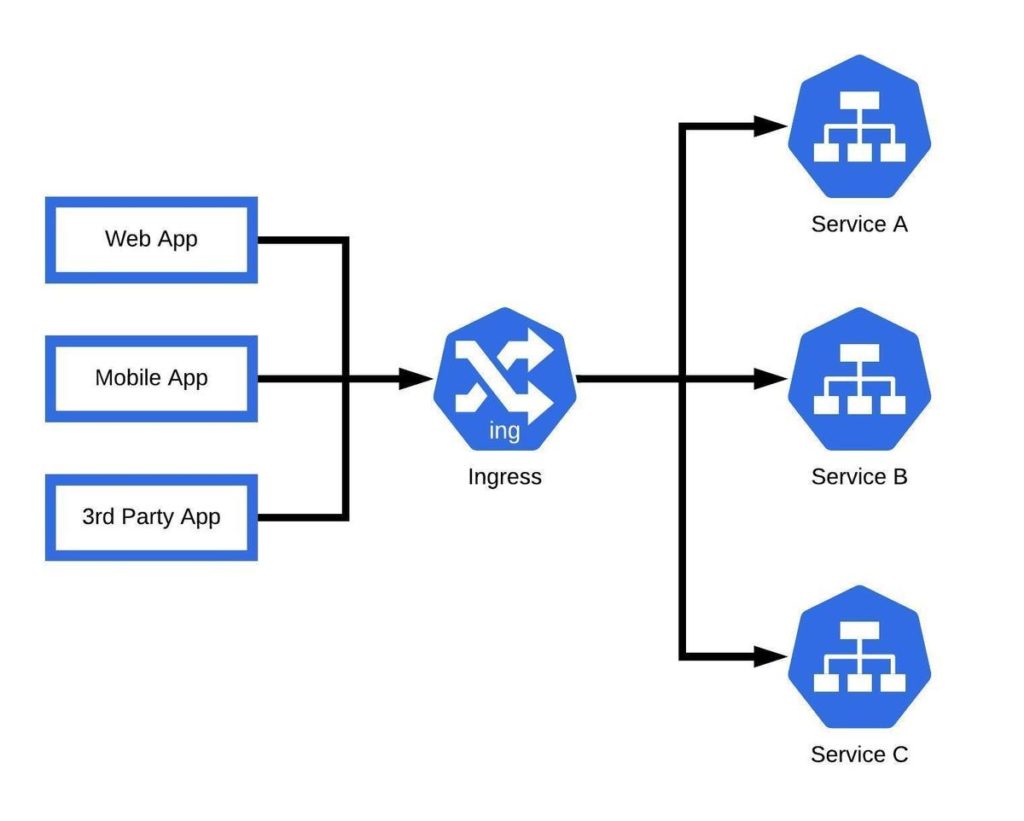
Docker containers and Kubernetes clusters are at the forefront of modern application deployment in containerization. Seccomp seamlessly integrates with these technologies to enhance security:
1. Docker Containers: By configuring seccomp profiles within Docker containers, you can ensure each container operates within its designated secure computing mode. This isolation prevents containerized applications from accessing unnecessary system calls, reducing the risk of exploits. Docker makes it relatively straightforward to specify seccomp profiles, even allowing you to use third-party profiles for added flexibility.
2. Kubernetes Cluster Security: In a Kubernetes cluster, the kubelet is essential in managing container runtimes. Enforcing seccomp profiles at the kubelet level allows you to maintain consistent security across all containers within your cluster. This centralized approach simplifies the management of seccomp profiles, ensuring that security policies are uniformly applied.
Benefits of Seccomp for Kubernetes Security
The implementation of seccomp offers several technical benefits, including:
- Reduced Attack Surfaces: By limiting system call access, seccomp reduces the potential attack vectors available to malicious actors.
- Enhanced Threat Mitigation: Seccomp helps mitigate threats by preventing unauthorized system calls, making it harder for attackers to compromise your containers.
- Enhanced Resilience: Seccomp fortifies Kubernetes environments, contributing to their resilience against security threats and promoting a safer containerized ecosystem.
Challenges and Considerations
While seccomp is a potent security tool, it comes with challenges and considerations:
- Configuration Complexity: Fine-tuning seccomp filters can be complex, demanding in-depth knowledge of system calls.
- Compatibility: Not all applications work seamlessly with strict seccomp profiles, and misconfigurations can lead to application failures.
- Maintenance and Updates: Regularly updating seccomp profiles for new features or kernel changes can be a maintenance challenge.
- Resource Intensive: Extensive system call filtering may consume significant resources, potentially impacting performance.
- Testing and Validation: Rigorous testing is crucial to avoid inadvertently blocking critical system calls, which could lead to application issues.
How to utilize Seccomp
Here’s how to maximize seccomp potential.
- Granular Control: Define precise system call permissions, reducing potential container exploits.
- Privilege Escalation Mitigation: Seccomp prevents privilege escalation attacks by blocking critical system calls.
- Untrusted Input Handling: Restrict system calls for containers handling untrusted input, mitigating risks from malicious data.
- Compliance and Standards: Seccomp supports compliance with industry regulations by enforcing security policies.
- Real-Time Monitoring: Detect and respond to unauthorized system call attempts in real-time with seccomp policies.
Conclusion: your ally in comprehensive Kubernetes security
Seccomp seamlessly integrates with broader Kubernetes security measures, enhancing the overall security posture of containerized applications. It reduces the attack surface of the Linux kernel, making it a fundamental component in kernel hardening strategies.