Best CSPM for Kubernetes: Why Posture Management Needs Runtime Context
You just connected your Kubernetes clusters to a CSPM tool. Within a few hours, the...
Secure your Kubernetes environment. Learn about K8s hardening, RBAC best practices, network policies, and how to defend against modern cloud-native threats.
You just connected your Kubernetes clusters to a CSPM tool. Within a few hours, the...
AI Agent Sandboxing Has a Definition Problem You’re in a Slack thread at 9 AM...
Every cloud security vendor now has an AI-SPM dashboard. Strip away the branding, though, and...

Your CISO just got word that engineering is deploying AI agents into production Kubernetes clusters...

Key Insights Why does traditional Kubernetes security fall short? Static scanners flag thousands of CVEs...
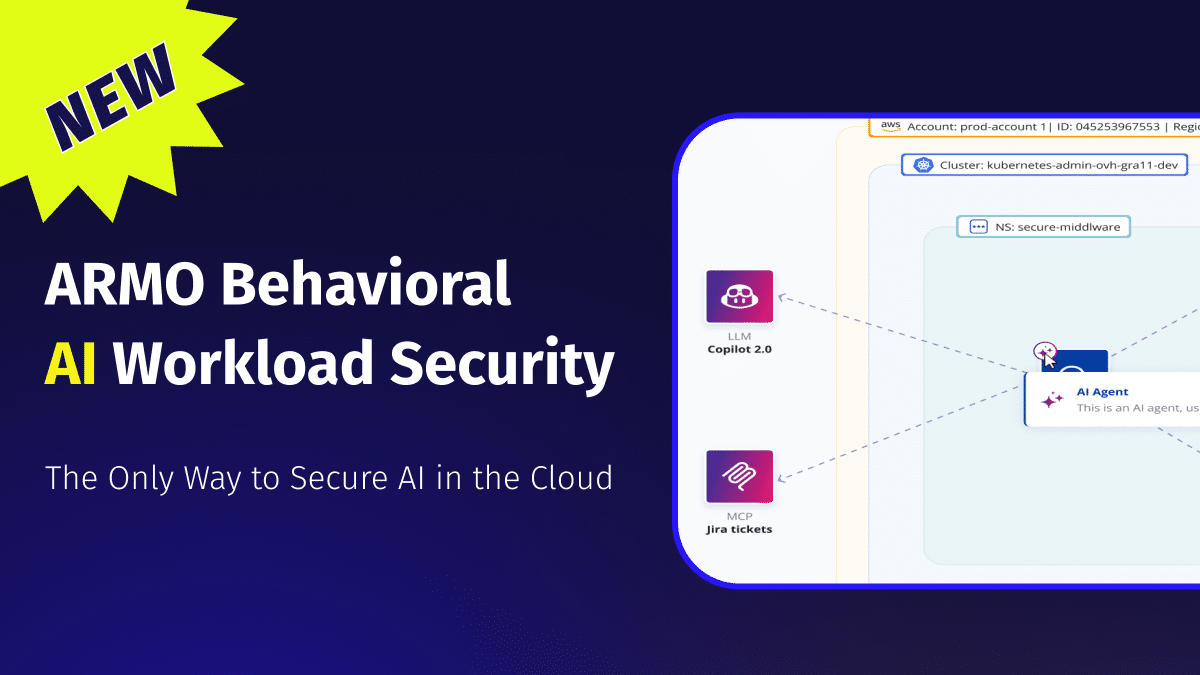
The Only Way to Secure AI in the Cloud AI is not just another workload...

Key Insights Why do most Kubernetes security tools fail teams in practice? Because they treat...

Key Insights What is container registry security? Container registry security is the set of practices,...

Key Insights Why do most Kubernetes security tools miss runtime threats? Most Kubernetes security tools...

Key Insights When your security team asks “What’s the best local Kubernetes tool?”, they usually...

Key Insights What is Kubernetes Security Posture Management (KSPM)? KSPM is the continuous process of...

Key Insights What is a Kubernetes dependency scanner? A Kubernetes dependency scanner finds known vulnerabilities...