CSPM
What is Cloud Security Posture Management?
Cloud Security Posture Management (CSPM) is the process of automating the security assessment and resolution process. CSPM tools enable organizations to persistently check for misconfigurations in their cloud which might lead to errors and security breaches in the company’s cloud infrastructure. CSPM tools automate the process across various verticals, including Infrastructure as a Service (IaaS), Software as a Service (SaaS), and Platform as a Service (PaaS).
Thus, CSPM tools enable organizations to continuously improve the cyber security of their cloud system by indicating the various flaws in the configuration. In the current scenario, these tools are critical as it allows companies to be updated with the latest compliance regulations, thus helping them build a more secure environment for their data and applications.
Challenges Companies Face without CSPM Tools
Compliance Issues
Compliance standards ensure the configurations are optimal for maintaining the security of the cloud. However, developers might overlook these standards, due to which infrastructures would be vulnerable to diverse threats and issues, as given below.
Security Breach
The cloud system might have certain errors and misconfigurations in the code, which attackers can exploit. Issues such as data theft, complete system downtime, and more can occur due to a security breach.
Unintentional Risks
Companies usually try to account for malicious attacks but might overlook unintentional issues such as the vulnerability of sensitive data. Without CSPM tools, this kind of risk cannot be spotted, troubleshot, and resolved.
Lack of Understanding of an Incident
Companies that do not use CSPM tools tend to have incidents that cannot be comprehended. Due to the lack of perimeter and centralization compared to on-premises systems, organizations struggle to find the cause of an incident. Hence, they are ill-equipped to deduce how the incident took place and the repercussions of the same.
How CSPM Solves Cloud Security Challenges
- Discovery of Cloud Workload:
At any instant, CSPM tools allow developers to have visibility on what is happening on the cloud. The tools offer a single information point across different cloud environments and accounts. Developers and other cloud users can have eyes on the resources, the paths, the configurations/misconfigurations, metadata, activity change, and more.
- Automatic Risk Assessment and Management:
CSPM tools assess the various configurations of the cloud infrastructure and evaluate the different resources, ports, app data, and more for risks. Once the tools spot them, they automatically manage and remediate them. Thus, the complete process is automated and requires minimal human intervention.
- Real-time Alerts:
Since CSPM tools automate processes, devops and security personnel get real-time alerts on the various activities occurring in the cloud infrastructure. Thus, at any instant, if a breach or any kind of incident is about to happen, devops engineers can mitigate and prevent it.
- Compliance Check:
CSPM tools conduct audit-like processes to check if the infrastructure meets compliance standards. This implies that all configurations will be reviewed, and if there is a misconfiguration, the tools will be able to solve the issue automatically.
- Policy Visibility and Enforcement:
CSPM tools enable the deployment of security policies across groups based on region, virtual networks, projects, users, and more. Furthermore, they help in the management once these policies are enforced and can be rewritten by personnel based on the changing needs.
CSPM vs. KSPM
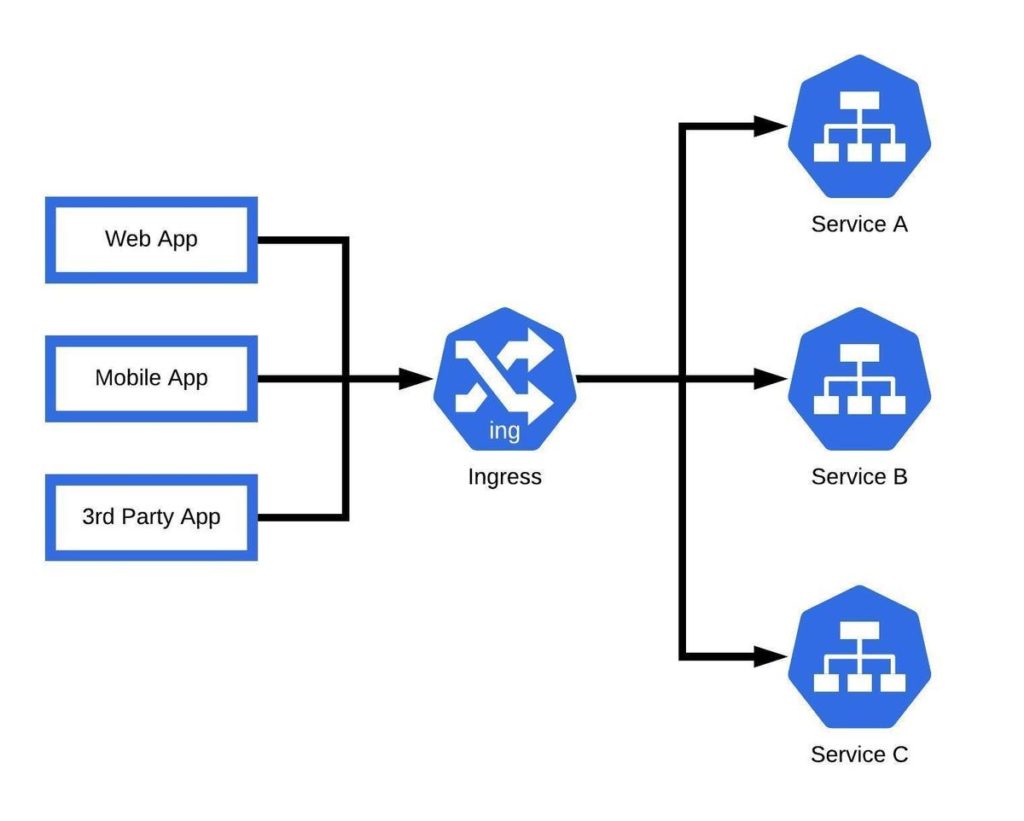
KSPM stands for Kubernetes Security Posture Management, and it is similar to Cloud Security Posture Management (CSPM) in many ways. However, CSPM and KSPM differ in the following:
- CSPM caters to all cloud environments, whereas KSPM caters only to the security of Kubernetes.
- CSPM checks for cloud compliance standards and recommendations, such as cloud networking policies and IAM policies. On the other hand, KSPM focuses on RBAC policies, container configurations, and more.
- While CSPM refers to clouds specifically, KSPM can also be applied to on-premises systems if Kubernetes is deployed in them.
Alternatives of CSPM
- CSPM vs. CISPA:
CISPA (Cloud Infrastructure Security Posture Assessment) is the initial version of the current CSPM tools. Although CISPA tools provided functionalities such as reporting errors and security risks, they did not help with remediation like CSPM. CSPM involves the usage of artificial intelligence and a guided process that helps with the resolution once a problem is spotted.
- CSPM vs. CWPP:
CWPP stands for Cloud Workload Protection Platforms and focuses solely on the workload aspect of cloud environments. CWPP works across providers and is an extension of anti-malware, application security, and more when it comes to the workload of an app. However, CSPM has a broader coverage as it focuses on the complete environment and not merely the workload.
- CSPM vs. CIEM:
Like CWPP, CIEM (Cloud Infrastructure Entitlement Management) focuses on a specific area of the cloud environment. CIEM tools monitor accounts that could potentially be involved in credential theft. Thus, in many ways, CIEM can be a part of CSPM, but since CSPM monitors the entire environment, the usage of CIEM becomes redundant.
How Does a CSPM Tool Work?
CSPM tools are integrated with different parts of the cloud infrastructure, such as dashboards, reports, backend functioning of the cloud, and more. It enables integration with multiple cloud providers such as Azure, AWS, and more. Once deployed, these would be able to collect all real-time configuration data, find misconfigurations, check for compliance, and fix issues.

Unifying AppSec, CloudSec and DevSec
The only runtime-driven, open-source first, cloud security platform:
Continuously minimizes cloud attack surface
Secures your registries, clusters and images
Protects your on-prem and cloud workloads