What is IAM? A Complete Guide
What is IAM?
Identity and Access Management (IAM) is a security framework for controlling the entities permitted to access an organization’s resources and the actions they can perform on the resources.
IAM aims to establish a strong foundation for information security by providing secure access to systems, applications and data. But why is this important, what are some benefits of IAM, and how does IAM work? We’ll explore these, top IAM best practices, and emerging IAM trends.
Why is IAM important?
IAM is important because it offers a robust defense against unauthorized access and data breaches. A well-implemented IAM programme offers enterprises the following key benefits.
Improved digital identity security: IAM includes components – like MFA and identity lifecycle management (ILM) – for securing digital identities. Digital identities here refer to the online representation of an individual or application. They include their login details, permissions, and identifier information. IAM secures digital identities to prevent identity theft and data breaches.
Enhanced Security Posture: IAM facilitates identity verification, enables user monitoring, and enforces strict access controls, minimizing the risk of unauthorized access.
Better Compliance: By enforcing strict access controls and tracking access activities, IAM ensures adherence to data protection standards such as PCI DSS (Payment Card Industry Data Security Standard) and HIPAA (Health Insurance Portability and Accountability Act).
It also lets enterprises create audit trails for compliance reporting and demonstrate dedication to protecting customer data.
Optimized User Access Management: IAM centralizes identity management into one single source of truth (SSOT). By doing this, it boosts secure data access, and streamlines ILM processes, e.g. provisioning.
Increased User Productivity: IAM concepts like Single Sign-On (SSO) and federated identity streamline user authentication. They reduce password fatigue and boost productivity by removing the need for multiple login credentials.
Core Elements of IAM
IAM core components aim to prevent unauthorized users from accessing enterprise resources. They also ensure legitimate users can seamlessly access approved resources. These components include:
1. Identity Management
Identity management covers various aspects of ILM, including user provisioning, update, and de-provisioning. Here’s what each means.
- Provisioning: IAM involves creating user identities, roles, and permissions to manage access to enterprise resources. It also defines the actions these entities can perform, such as reading, writing, or deleting data.
- Update: Modifying user roles, attributes, and permissions as job roles change.
- De-provisioning: Deleting digital identities and corresponding access rights when they are no longer necessary, e.g., when an employee leaves or a project gets completed.
2. Authentication
Authentication ensures users prove that they are who they claim before they are granted access. Authentication mechanisms include:
- Passwords: Uses a username/password pair to verify entities before granting access. IAM systems enforce password policies, such as periodic password changes and complexity requirements (e.g., using multiple character types) to make passwords harder to break and enhance security.
- Multi-factor authentication (MFA): Uses two or more authentication methods, including something the user knows (e.g., a password), something they are (e.g., biometrics), and something they have (e.g., an OTP).
- Passwordless authentication: Authenticates users using biometrics, cryptographic keys, or token exchange. For example, cloud service providers like AWS and Azure offer passwordless sign-in via FIDO2 passkeys.
3. Authorization
Authorization ensures you have the necessary role or attributes to access specific resources. Authorization models include:
- Role-based access controls (RBAC): Assigns permissions based on user roles; e.g. in a healthcare setting, a doctor would have ‘write’ access to patient medical records and prescriptions while a nurse would typically have ‘read’ access.
- Attribute-based access controls (ABAC): Grants granular access based on user attributes, incorporating real-time considerations rather than static user roles; e.g. further limiting doctors’ access to patient’s records based on business hours or IP geolocation.
- Policy-based access controls (PBAC): Grants access based on predefined rules and policies; e.g., allowing doctors Write access only to medical records of inpatients under their care, while within enterprise network perimeters.
- Just in time (JIT) access: Temporarily elevates user privileges to allow access to sensitive assets needed to complete a task. Privileges are revoked once the task is completed.
4. Federated Identities
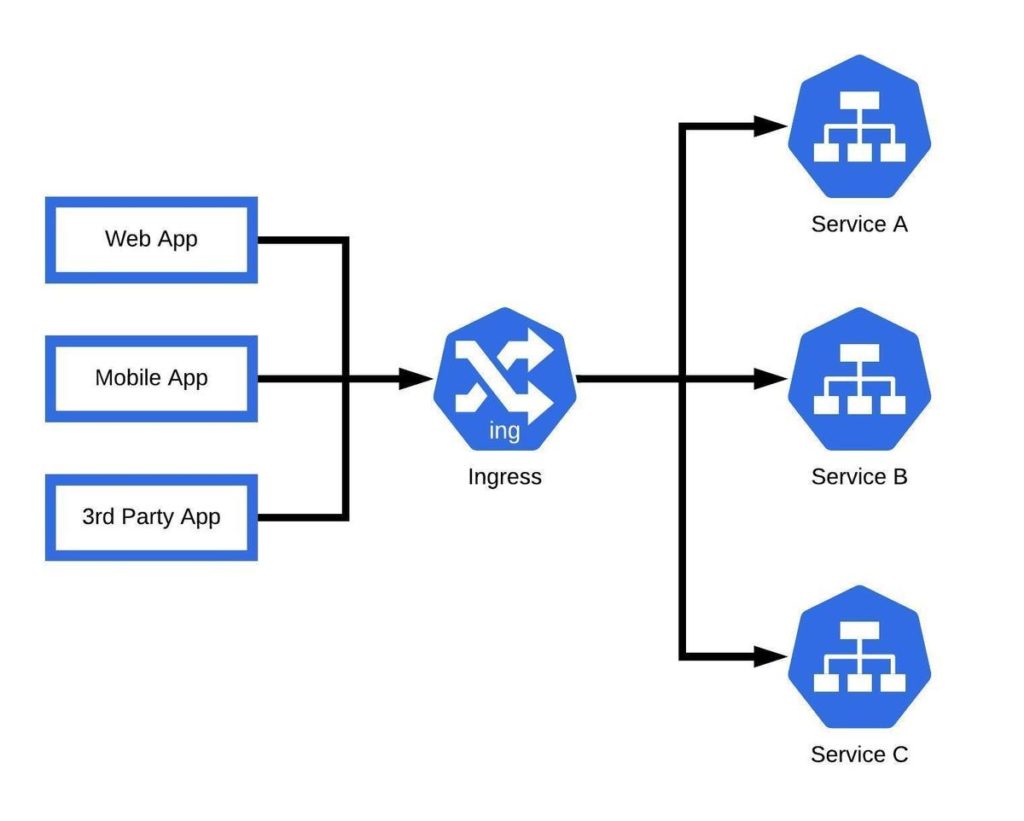
Federated identities let users authenticate once with a single identity provider (IdP) and access multiple interconnected services. A common example is the sign-in-with-Google feature on apps like LinkedIn, Slack, and Twitter.
5. Single Sign-On (SSO)
SSO allows users to access multiple resources within an organization using a single set of credentials. This reduces the likelihood of weak passwords and password reuse, which are common attack vectors for brute force attacks. A common implementation of SSO is that signing in to Google automatically gives access the the full Google suite.
6. Identity Governance
Identity governance involves tracking user activity before, during and after authentication and authorization. Identity governance creates audit trails of user activity around sensitive information, which facilitates compliance and enables enterprises to detect suspicious behavior.
7. Zero Trust
Zero-trust is based on the notion that everyone’s-a-threat-until-proven-otherwise. It requires users to continuously verify their identity and access rights, even when within the enterprise’s networks.
Zero-trust is the opposite of the traditional perimeter security model, which only secured external perimeters from unauthorized access. The traditional approach assumed that everything behind an organization’s firewalls was safe. Zero-trust’s requirement for continuous authentication, curtails lateral movement and insider threats.
8. Principle of Least Privilege (POLP)
POLP is a granular implementation of RBAC; it mandates that users only get the minimum access required to execute their roles.
How IAM works
IAM works as a step-by-step process from provisioning to authentication, authorization, auditing, and deprovisioning. Here’s a closer look.
User provisioning: Can be automated via tools like SCIMs (System for Cross-domain Identity Management) or manual where an admin manually registers a new identity/role to a directory e.g., Microsoft Active Directory.
Authentication and Authorization: Once identities are created, IdPs use any of the various authentication methods available to verify users and ensure they only have access to resources based on predefined access controls.
Auditing and Monitoring: Involves integrating advanced monitoring and analytics tools for threat detection and Security Information and Event Management (SIEM) platforms for compliance audit trail collection.
Deprovisioning: This is the last leg of ILM; involves deleting orphaned or unnecessary accounts to prevent identity sprawl.
Challenges of Implementing IAM
Top challenges enterprises face implementing IAM include:
Balancing over-permissioning and under-permissioning
Excessively strict access controls can frustrate users into bypassing authentication or creating shadow identities (unmonitored identities with permissions enterprises can’t control). On the flip side, overly permissive controls can allow unfettered access to cybercriminals. So ensure the right balance between both by implementing POLP.
Managing IAM across hybrid and multi-cloud environments
Cloud security alliance reports that 60% of organizations find the complexity of their environments a hindrance to effective IAM. Top reasons for this include challenges synchronizing identities and inability to maintain access policy consistency across varied environments. To solve this, deploy interoperable IAM solutions capable of unifying hybrid and multi-cloud IAM.
Authentication Security Concerns
As cyberattackers adapt to new IAM mechanisms, developing increasingly sophisticated attack techniques, enterprises face ongoing challenges establishing secure authentication methods. MFA and zero-trust come in handy here, effectively increasing the difficulty level and ensuring attackers cannot bypass all authentication mechanisms.
Integration Hurdles
Choose flexible IAM solutions to prevent integration problems.
Top IAM Best Practices
For a successful IAM program, adopt the following best practices.
- Continuously review user access rules to prevent privilege creep – a situation where users gain unnecessary privileges over time.
- Adopt RBAC, ABAC and PBAC complimentarily, taking into consideration static roles and policies, as well as real-time attribute changes. This locks out users who don’t meet all access requirements, further cutting the chances of unauthorized access.
- Automate provisioning and deprovisioning to prevent identity drift and permission sprawl.
- Deploy proper privileged identity management (PIM) and privileged access management (PAM) to restrict access to privileged accounts and safeguard sensitive resources – anyone with access to privileged accounts can make critical changes and hold systems to ransom.
- Activate predictive IAM by monitoring baseline behavior and anticipating/responding to anomalies in real time.
- Regularly review access logs to detect and investigate suspicious activities early: great as monitoring tools are as first responders, they may not pick up on threats if no obviously untoward access activities (like privilege escalation or a change in IP location) are noticed.
- Train employees and create security awareness: Phishing is real and anybody can fall for it.
Emerging Trends in IAM
As IAM adoption rises, innovations continue to emerge to enhance identity security and data protection.
One of such emerging IAM trends is adaptive authentication. Authentication used to be static; remaining the same, regardless of IP changes or multiple failed login attempts.
But as such changes have become common vectors for identity-based attacks, enterprises are starting to apply adaptive MFA where increasingly difficult authentication mechanisms are applied when login attempts seem suspicious.
Passwordless authentication is also growing in popularity. Enterprises are adopting biometrics, passkeys, and other authentication mechanisms in favor of the more attack-susceptible passwords.
Another development is the emergence of non-human identities (NHIs), a result of cloud and AI adoption. These identities, including service accounts, apps, bots, and APIs, require access to sensitive resources to complete their tasks. Rigorous authentication/authorization processes must be applied to them to ensure data security.
Additionally, attacks like phishing are becoming increasingly difficult to evade, thanks to AI innovations. Conversely, AI advancements and AI security concerns – like model poisoning and data exposure – are also driving IAM, fueling predictive IAM, AI-powered threat detection, and adaptive authentication.