Container Security
With so many companies going cloud-native for their apps and architecture, containers have never been more popular. A recent Gartner report predicts that by the end of 2022, 75% of organizations worldwide will have containerized applications running within their infrastructure. With containers continuing to go mainstream, getting better at securing them is a growing priority for many organizations. That presents a challenge because containers can be a bit more challenging to secure than other implementations and many organizations that adopt containers for the first time don’t have the scanning tools and competencies to manage them effectively. Ensuring that containers are secure and isolated while simultaneously ensuring availability, performance, and integrity is no easy feat.
What is container security?
Container security represents using security tools, policies, and methodologies to protect container-based workloads from unauthorized access and malicious attacks. Not limited to just the containers themselves, it refers to resources in the cloud or on-premises like infrastructure, runtime environments, software applications that have mutual dependencies with containers.
One of the main benefits of containers is how seamlessly they integrate into DevOps pipelines for automated integration, testing, and deployment. Unfortunately, these valuable characteristics present attack surfaces that many organizations don’t fully grasp. Let’s take a look at some of the main challenges.
The Main Challenges of Container Security
Containers empower developers to quickly deliver capability with speedy, automated deployments into the customers’ hands. That also means containers with vulnerabilities get into production faster and more frequently. Developers often tout containers to isolate their workloads, but this also means container access exposes its contents to potential vulnerabilities and exploits. Misconfigurations, trust issues, or image and code vulnerabilities can potentially expose containers to attacks.
Another common complication is that every cloud provider has different native security tools, and many micro-service-oriented applications that rely on containers have components spread across multiple clouds or in on-prem implementations. On top of that, different architectures and design patterns will raise unique security constraints and requirements. Security teams need to manage all of this while minimizing impacts to the developer deployment lifecycle.
Best Practices for Container Security
Here are some best practices for maintaining container security:
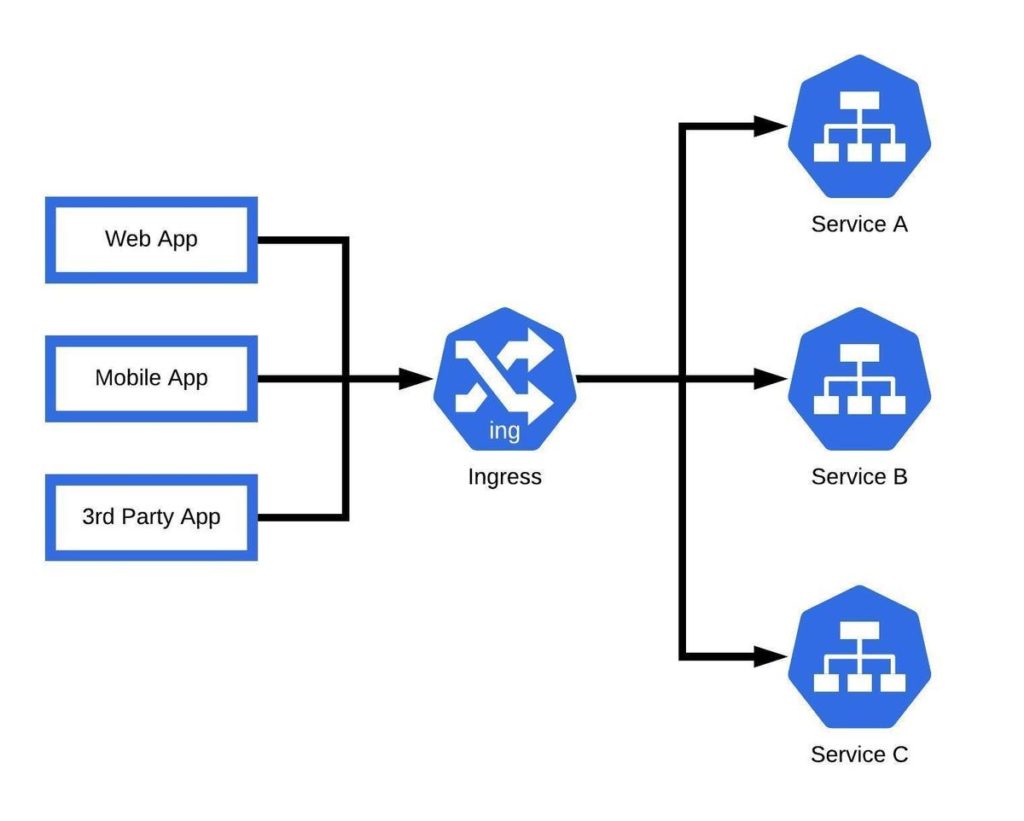
Network Security and Policies
Containers are the cornerstone of microservice-oriented architectures. While powerful and highly beneficial, these architectures increase data traffic by exposing many services to the network. Poorly implemented privileges or privilege escalation attacks pose a significant threat to containerized environments because all the services need to be accessed for the applications to function correctly. Security teams and developers must configure container applications, and processes with the minimum required permissions to work as designed. In addition, traffic should be secured through firewalls, service mesh, mTLS, identity-based zero trust, and microservice communications should be secured via micro-segmentation.
Runtime Security
Runtime Security is the art and science of protecting workloads against threats while containers run in production. Attackers attack containers during runtime by exploiting vulnerabilities to deploy unauthorized containers, exploiting misconfigurations to gain access to sensitive information, or hiding malware within container images. Organizations seeking to secure their containers during runtime should leverage tools to manage Kubernetes Secrets and leverage zero-trust policies wherever possible.
Control Plane Hardening
In Kubernetes, the control plane is responsible for maintaining the desired end states of the cluster as defined by the developer. The two key elements of control plane hardening are container image assurance and avoiding misconfigurations. Container images must be scanned for vulnerabilities and digitally signed before entering container registries. Developers and security teams should verify security policies and configurations before containers enter the CI/CD pipeline.
App Security
Just because an application is implemented with a microservice architecture or containerized doesn’t mean we don’t have to worry about application and code security. Developers should maintain code security with continuous vulnerability scanning throughout the lifecycle. Third-party tools and libraries should also be scanned and verified before integrating into any application.