Microservices Security
What is microservice security?
Customer and business expectations have never been higher in today’s software world. The continual transition from monolithic architectures to microservices helps developers deliver larger, more complex systems to customers in a fraction of the time. 2021 surveys show that 37% of software organizations have adopted microservices. Microservice-oriented architecture brings many benefits, but it also introduces unique challenges, particularly in the security dimension.
What are microservices?
Microservices- sometimes called microservice-oriented architecture- refers to structuring and organizing applications as a collection of services. What distinguishes it from earlier iterations of service-oriented architectures are these common characteristics:
- Must be easy to maintain and test. Services should be able to be replaced entirely instead of patched and updated.
- They are loosely coupled, with communications occurring via APIs rather than integrated with internal mechanisms and calls.
- They should be individually deployable, with minimal outside dependencies impacting implementation.
- They should be functionally and business-oriented, working standalone to deliver actual capability and value.
When done correctly, microservices are a central pillar of DevOps CI/CD delivery modes, ensuring frequent and reliable delivery of complex systems. Unfortunately, it comes with a cost. Microservice architecture may expose hundreds of potentially vulnerable endpoints instead of a single or handful of entry points like a monolithic application. Even though these systems are supposed to be loosely coupled, a sophisticated attacker could eventually compromise an entire system with unauthorized access to even a single service.
Best Practices for MicroService Security
Access Control
Access control is a significant part of securing microservices with many endpoints to manage. Organizations should leverage Role-Based Access Control (RBAC) policies and best practices for user authentication, like implementing OAuth authorization.
Scan Code and all Dependencies
Code scanning is a critical component of all application security, and microservice architectures don’t change that. Any vulnerabilities in external services or libraries could act as a backdoor into your system. Organizations should also consider scanning any third-party or open-source components their microservices use.
Security Testing
Both known and unknown security vulnerabilities rise year over year. Every software developer needs a robust testing program in-house, which they should integrate across every DevSecOps CI/CD pipeline stage. Organizations should leverage both static and dynamic application tests and test their microservices during runtime.
Container Security
Microservices use containers. That makes maintaining secure containerized environments critical to microservice security. To secure containers, security teams need to focus on network security and policies, runtime security, and the security of the application itself. For K8s implementations, control plane hardening is another critical factor.
API Security
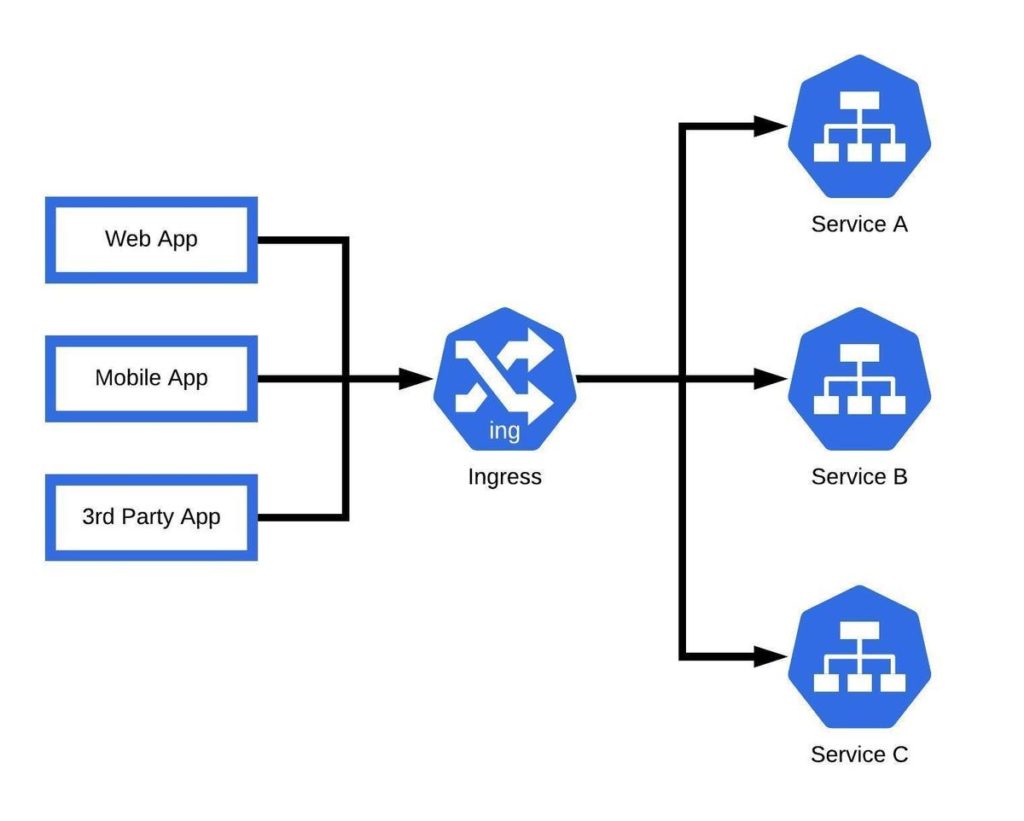
APIs provide the means for microservices to communicate with each other. That makes them one of the most vulnerable components of the architecture. Leveraging API gateways is considered a best practice as it helps secure these interfaces by allowing communications to take place without giving clients direct access to the services themselves.
Service Mesh
Service mesh is critical for securing distributed applications like those built with microservices. Among other features, they enable authentication controls for interservice communications. They also help ease the burden of managing many services, reducing workloads and the misconfigurations that result.
Securing a Cluster in Kubernetes
For Kubernetes implementations, securing clusters is the center point of maintaining your microservice architecture. There are some helpful guidelines that security teams and developers must be aware of to assure their microservices in Kubernetes remain secure.
- Kubernetes expects TLS encryption on all API communications within a cluster.
- All API clients must be authenticated.
- Kubelets expose HTTPS endpoints, which can make nodes and containers vulnerable. Since Kubelet allows unauthenticated access to this API, developers should make sure they enable Kubelete authentication and authorization for their production implementations.
- Make sure that network policy restrictions apply to pods and ports within the cluster.
Microservice Security with Kubescape
Microservice architectures are already becoming mainstream, and many of these systems reside within Kubernetes environments. Kubescape can help system admins and security teams manage their microservices securely. It helps detect misconfigurations and software vulnerabilities at the early stages of the CI/CD pipeline, so they never make it into production. Sophisticated alerts and visualization tools help teams continuously assess risk and harden their infrastructure against attacks. To find out more, sign up or watch a demo.