AI Security Posture Management (AI-SPM): The Complete Guide to Securing AI Workloads
Every cloud security vendor now has an AI-SPM dashboard. Strip away the branding, though, and...

Jan 8, 2026
Your morning scan returns 3,000 CVEs. Maybe a dozen actually matter. But which dozen?
You’re running Trivy for image scanning, Falco for runtime detection, kube-bench for compliance, and Calico for network policies. Each tool generates alerts in its own format, its own dashboard, with its own context. When an incident happens, connecting a vulnerable image to a misconfigured RBAC role to a suspicious process requires manual work that doesn’t scale past a handful of clusters.
This guide takes a different approach. Instead of another feature list, we’ll walk through 12 open-source Kubernetes security tools organized by what actually matters: runtime context first, then the scanning and policy tools that feed into it. You’ll learn what each tool does, where it fits in your stack, and how to combine them without drowning in noise.
Most security tools create noise. They flag thousands of issues without telling you which ones actually matter in your environment. Research shows 78% of CVEs reported for container images can be deprioritized through contextual analysis. The question isn’t whether a vulnerability exists—it’s whether it’s exploitable in your specific production environment.
Static scanners check your manifests and container images for known issues. They’re useful, but they can’t tell you which vulnerabilities are actually loaded into memory and executed in production.
Tools with runtime awareness watch what your applications actually do. They distinguish between a CVE in a library that’s never called versus one actively processing requests. This is reachability analysis—understanding which code paths attackers can actually reach. When applied properly, runtime reachability typically reduces the CVE count you need to act on by 90% or more.
Security findings without fix guidance create backlogs. Findings that break applications when fixed create distrust between security and platform teams.
Effective tools analyze actual workload behavior to identify which changes are safe. They establish a behavioral baseline—what your application normally does—so you can make changes with confidence instead of guessing. This is the difference between “this CVE exists” and “you can safely update this package without impacting production.”
Detection tells you something happened. Prevention stops it from happening.
Look for tools that can generate and enforce network policies, seccomp profiles (which limit what system calls containers can make), and admission controls based on observed behavior. The best tools use runtime data to automatically create prevention policies that are tailored to your specific workloads—not generic templates that either break things or leave gaps.
Tools built specifically for Kubernetes understand namespaces, pods, deployments, and RBAC natively. They deploy as DaemonSets or operators and scale with your cluster.
Adapted legacy tools often miss Kubernetes-specific context. They might see a process running but have no idea which pod, namespace, or service account it belongs to—limiting their usefulness for investigation and response. Modern eBPF-based tools typically add minimal overhead (1-2.5% CPU and ~1% memory consumption), making them practical for production deployments.
The Cloud Native Computing Foundation (CNCF) provides an objective maturity framework for evaluating open-source projects:
CNCF status isn’t everything—Trivy and Tetragon are excellent tools without CNCF membership—but it provides independent validation of project health and community support.
Before diving into individual tools, use this guide to identify where to start based on your specific challenges:
| If you’re struggling with… | Start here |
|---|---|
| Too many CVEs, no idea which are exploitable | Kubescape (runtime reachability) + Trivy (CI/CD scanning) |
| Detecting attacks and anomalies at runtime | Kubescape (detection + response) or Falco (detection) or Tetragon (detection + enforcement) |
| Misconfigurations and compliance gaps | Kubescape, kube-bench, Checkov |
| Blocking bad deployments before they happen | OPA/Gatekeeper or Kyverno |
| Limiting blast radius through network segmentation, network policies or seccomp profiles | Kubescape (network policies and seccomp profiles), Cilium (eBPF/L7) or Calico (standard NetworkPolicy) |
| Correlating alerts across your entire stack | ARMO Platform (extends Kubescape with full-stack correlation) |
| Tool | Primary Function | Domain | CNCF Status | Best For |
|---|---|---|---|---|
| Kubescape | Comprehensive security platform | Posture + Runtime | Incubating | Foundation for K8s security |
| Falco | Runtime threat detection | Runtime | Graduated | Rule-based detection |
| Tetragon | eBPF observability & enforcement | Runtime | — | Deep kernel visibility |
| Trivy | Vulnerability & config scanning | Image/Config | — | All-in-one scanning |
| Grype | SBOM-based vuln scanning | Image | — | Supply chain focus |
| kube-bench | CIS Benchmark validation | Compliance | — | Cluster hardening |
| Checkov | IaC security scanning | Shift-left | — | Pre-deployment checks |
| KubeLinter | Manifest linting | Shift-left | — | CI/CD integration |
| OPA/Gatekeeper | Policy enforcement | Admission | Graduated | Custom policy needs |
| Kyverno | K8s-native policy management | Admission | Incubating | YAML-based policies |
| Calico | Network policy & segmentation | Network | — | Multi-cloud networking |
| Cilium | eBPF networking & security | Network | Graduated | L7 policies, identity-aware |
We’re starting with runtime tools deliberately. Runtime is where attacks actually happen—and where context separates theoretical risk from exploitable vulnerabilities. Research from Red Hat found that 45% of organizations experienced runtime security incidents in the past 12 months. Unlike static scanners, runtime tools can identify threats that only manifest when code executes, including zero-days, supply chain compromises, and insider threats.
Most modern runtime tools use eBPF (extended Berkeley Packet Filter) to observe kernel-level activity without modifying applications or requiring sidecars.
Why Kubescape leads this list: While most tools in this guide focus on a single function, Kubescape is the only fully open-source platform that spans the complete Kubernetes security lifecycle—from CI/CD scanning to runtime detection to compliance reporting. With 11,000+ GitHub stars and adoption by 100,000+ organizations across 1,000,000+ deployments, it’s the most comprehensive open-source option available.
Kubescape scans clusters, manifests, and Helm charts against 260+ purpose-built Kubernetes security controls covering NSA-CISA, MITRE ATT&CK, CIS Benchmark, SOC2, PCI-DSS, and GDPR frameworks. But what sets it apart is runtime context.
Runtime reachability analysis identifies which vulnerabilities are actually loaded into memory and executed during runtime—not just which ones exist in your images. This typically reduces the CVE count you need to act on by 90% or more, cutting through thousands of theoretical vulnerabilities to surface the dozens that represent actual risk.
Key capabilities:
Kubescape is also the foundation for ARMO’s platform, which extends it with full-stack attack correlation and smart remediation capabilities.
Falco is the de facto standard for Kubernetes runtime threat detection. It uses a rules engine to detect suspicious behavior: unexpected process execution, file access, network connections, and syscall patterns.
Falco integrates with Kubernetes audit logs to correlate API server events with container activity. Falcosidekick extends alerting to dozens of destinations including Slack, PagerDuty, and AWS Security Hub.
Limitation: Falco is detection-only—it doesn’t provide remediation guidance or vulnerability context. Works well paired with Kubescape for comprehensive coverage.
Tetragon is an eBPF-based security observability and runtime enforcement tool from the Cilium project. It provides deep visibility into process execution, file access, and network activity at the kernel level.
Unlike detection-only tools, Tetragon can enforce policies and block malicious activity in real-time using LSM (Linux Security Module) hooks. It integrates naturally with Cilium for combined network and runtime security.
Image scanning tools analyze container images for known vulnerabilities (CVEs), misconfigurations, exposed secrets, and software bill of materials (SBOM). They’re critical for supply chain security—but their effectiveness depends entirely on whether you can distinguish exploitable vulnerabilities from theoretical risks.
This is where runtime context becomes essential. A scanner might flag 500 CVEs in an image, but if only 12 of those vulnerabilities exist in code paths that are actually executed in production, those 12 are the ones that matter. Pair these tools with runtime-aware platforms like Kubescape for effective prioritization.
Trivy is an all-in-one scanner covering container images, filesystems, Git repositories, Kubernetes clusters, and IaC files. It detects vulnerabilities, misconfigurations, secrets, and license issues in a single tool.
Trivy generates SBOMs in SPDX and CycloneDX formats for supply chain transparency. Fast scanning with offline database support makes it practical for air-gapped environments.
Best practice: Use Trivy in CI/CD pipelines for shift-left scanning, paired with Kubescape’s runtime reachability for production prioritization.
Grype is a vulnerability scanner designed to work with Syft-generated SBOMs for accurate dependency analysis. It focuses specifically on vulnerability matching with regularly updated feeds.
Lightweight and fast, Grype is well-suited for CI/CD pipeline integration where scan speed matters. Best for teams with a strong focus on supply chain security and SBOM-driven workflows.
Configuration scanning tools identify misconfigurations in Kubernetes manifests, cluster settings, and RBAC configurations. Misconfigurations account for a significant portion of Kubernetes security incidents—these tools help catch them before they become attack vectors.
Note: Kubescape (covered in the Runtime section) also provides comprehensive configuration and compliance scanning with 260+ controls. The tools below are more specialized options for specific use cases.
kube-bench checks Kubernetes clusters against the CIS Kubernetes Benchmark—the industry standard for cluster hardening. It runs as a job in your cluster and validates control plane, etcd, kubelet, and node configurations.
This tool is particularly valuable when compliance requirements mandate CIS benchmark adherence.
Limitation: Point-in-time auditing only—doesn’t provide continuous monitoring. Consider pairing with Kubescape for ongoing compliance tracking.
Checkov is an infrastructure-as-code security scanner supporting Kubernetes manifests, Helm charts, Terraform, CloudFormation, and more. It includes over 1,000 built-in policies and supports custom policy creation.
Ideal for shift-left security—catching misconfigurations before deployment rather than discovering them in production.
KubeLinter is a static analysis tool focused specifically on Kubernetes YAML files and Helm charts. It checks for security misconfigurations and DevOps best practices with fast, lightweight execution.
Easy CI/CD integration makes it suitable for pull request checks where you want quick feedback without slowing down developers.
Admission controllers intercept requests to the Kubernetes API server before objects are persisted, enabling policy enforcement at deployment time. Policy-as-code approaches allow security requirements to be version-controlled, tested, and applied consistently across clusters.
OPA is a general-purpose policy engine; Gatekeeper is the Kubernetes-native implementation. Policies written in Rego language offer maximum flexibility but require learning a new syntax.
ConstraintTemplates define reusable policy logic; Constraints apply them to specific resources. Audit mode allows testing policies against existing resources before enforcement.
Kyverno is a Kubernetes-native policy engine using familiar YAML syntax instead of Rego. It supports validate, mutate, generate, and verify image policies.
The learning curve is significantly lower than OPA for teams already comfortable with Kubernetes manifests. Policy reports provide visibility into compliance status across clusters.
When to choose Kyverno vs. OPA: Use Kyverno when your team prefers YAML and your policy requirements are straightforward. Use OPA/Gatekeeper when you need maximum flexibility or have complex policy logic that benefits from Rego’s expressiveness.
Network policies control traffic flow between pods, namespaces, and external endpoints—essential for limiting blast radius when workloads are compromised. Default Kubernetes networking allows all pod-to-pod communication; explicit policies are required to implement least-privilege network access.
Calico is an industry-standard network policy implementation supporting Kubernetes NetworkPolicy plus extended GlobalNetworkPolicy resources. It works across multiple cloud providers and on-premises deployments.
Cilium is eBPF-powered networking providing L3/L4 and L7 policy enforcement. Identity-aware policies use Kubernetes labels rather than IP addresses—critical for dynamic environments where pod IPs change frequently.
Hubble provides network observability with flow logs and service maps. ClusterMesh enables consistent policies across multiple clusters.
You now have Kubescape scanning configurations, Trivy checking images, Falco watching runtime, and Cilium enforcing network policies. Each tool generates alerts in its own format, its own dashboard, with its own context.
When an actual attack happens, it doesn’t stay in one layer. A real incident might look like this:
With siloed tools, you get four separate alerts in four dashboards with no connection between them. Your team spends hours manually correlating timestamps and piecing together what happened. By the time you understand the full picture, the attacker has moved on.
This is the gap that individual tools—no matter how good—can’t solve on their own. Correlation across the stack is what transforms scattered alerts into actionable attack stories.
Based on the tools covered, here are three proven patterns for building an effective Kubernetes security stack:
Tools: Kubescape + Trivy
Tools: Kubescape + Falco + Cilium
Tools: Kubescape + OPA/Gatekeeper + kube-bench
Start with your threat model: What are you protecting, and from whom? Compliance requirements often dictate baseline tooling—kube-bench for CIS, Kubescape for NSA-CISA.
Consider operational maturity. Teams new to Kubernetes security should start with configuration scanning and runtime context (Kubescape) before adding specialized detection layers. Adding tools without the foundation to interpret their output just creates more noise.
Key evaluation criteria:
Open-source tools excel at specific functions but require integration effort to correlate findings across layers. A CVE alert from Trivy, a misconfiguration from Kubescape, and a runtime anomaly from Falco may all relate to the same attack chain—but connecting them manually is time-consuming and error-prone.
ARMO is built on Kubescape, the open-source project trusted by 50,000+ organizations. It extends Kubescape’s foundation with the correlation layer that individual tools can’t provide:
See runtime intelligence in action: Watch a demo of how ARMO correlates signals across your stack to show complete attack stories.
Open-source tools provide strong coverage for specific security functions—Kubescape for posture and compliance, Falco for runtime detection, Trivy for scanning, OPA for policy enforcement. For many organizations, a well-integrated open-source stack meets their security requirements.
Commercial platforms add value through correlation across tools, managed updates, support SLAs, and features like automated remediation and attack story generation. The decision depends on your team’s capacity to integrate and maintain open-source tools versus the value of turnkey correlation and support.
Alert fatigue typically stems from tools that flag theoretical risks without runtime context. Three strategies help:
First, prioritize tools that provide context-aware findings. Runtime reachability analysis (available in Kubescape) identifies which vulnerabilities are actually loaded and executed—this alone can reduce actionable CVE counts by 90% or more.
Second, apply risk scoring based on actual exposure: Is the workload internet-facing? Does it have privileged access? Does it access sensitive data?
Third, correlate alerts across tools. Four separate alerts that relate to the same attack chain should be one investigation, not four.
eBPF-based tools (Falco, Tetragon, Kubescape’s runtime sensor, Cilium) typically consume minimal resources—in the range of 1-2.5% CPU and approximately 1% memory per node. This makes them practical for production deployments.
However, running multiple DaemonSets adds cumulative overhead. Best practice: test in staging, monitor resource consumption, and consolidate where possible. Platforms like ARMO that combine multiple functions (posture + runtime + compliance) in a single agent can reduce total overhead compared to running separate tools for each function.
Focus on vulnerabilities with three characteristics:
1. Actually exploitable based on runtime reachability: Is the vulnerable code loaded and executed? Many CVEs exist in libraries that are included but never called.
2. Exposed to attack paths: Is the workload internet-facing, privileged, or accessing sensitive data? A CVE in an internal batch job is lower risk than the same CVE in your API gateway.
3. Actively exploited in the wild: Check CISA’s Known Exploited Vulnerabilities (KEV) catalog and EPSS scores for exploitation probability.
Tools that combine static scanning with runtime context (like Kubescape with ARMO’s runtime intelligence) can surface this prioritization automatically—cutting thousands of theoretical CVEs down to the dozens that represent actual risk, with remediation guidance that accounts for your workload’s actual behavior.
Every cloud security vendor now has an AI-SPM dashboard. Strip away the branding, though, and...

Your security stack was built for workloads that follow predictable code paths. AI agents don’t....
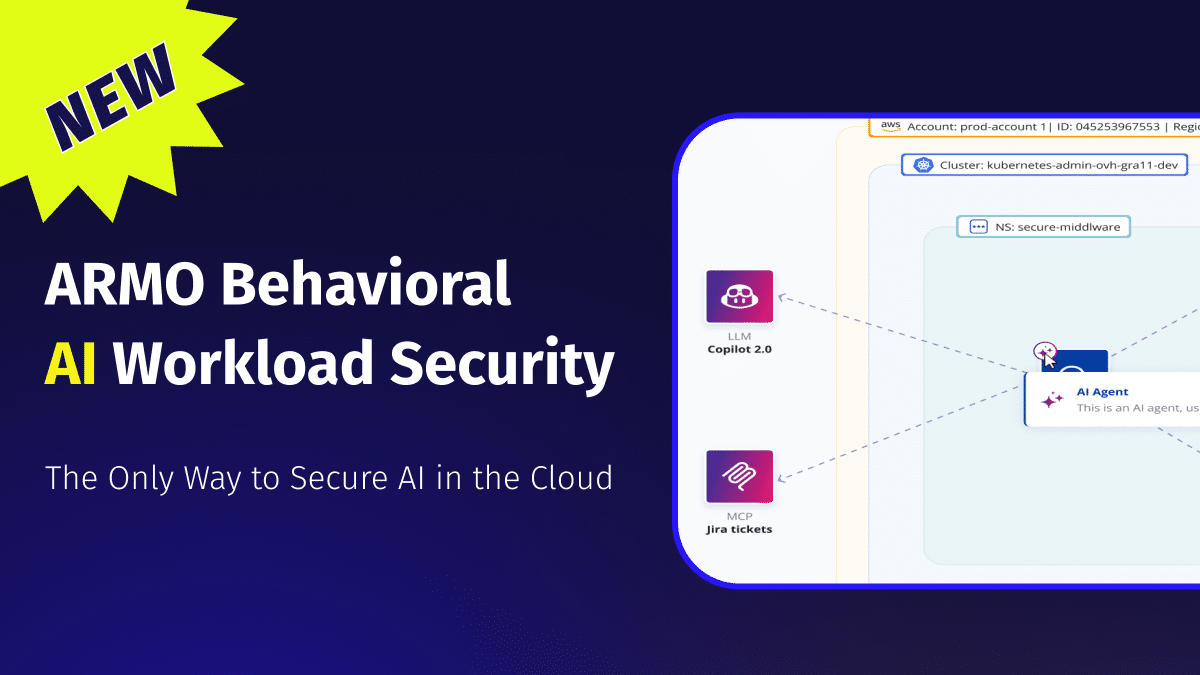
The Only Way to Secure AI in the Cloud AI is not just another workload...