Block the attack paths into your Kubernetes clusters
Discover the importance of mapping attack paths in Kubernetes and learn how to effectively enhance...
Secure your entire cloud-native lifecycle. Explore strategies for protecting code, containers, clusters, and clouds using Zero Trust and automated governance.
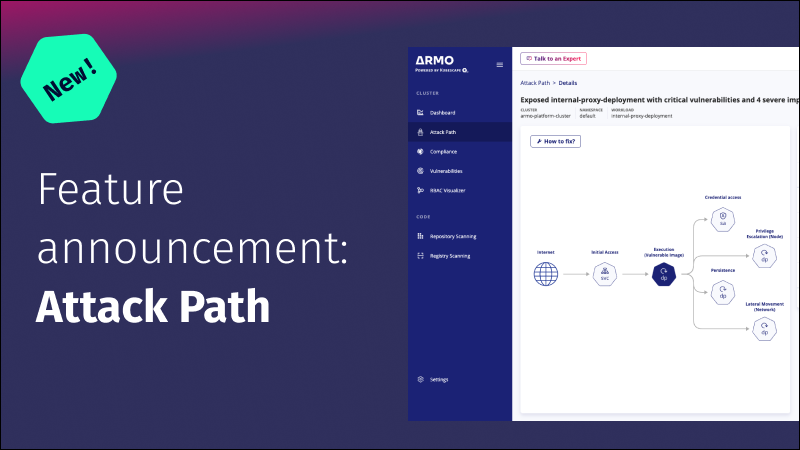
Discover the importance of mapping attack paths in Kubernetes and learn how to effectively enhance...
Kubernetes misconfigurations can create security risks and other issues. This article covers common types, their...

Kubernetes has become the de facto platform for orchestrating containerized applications at scale in today’s...

Guest post originally published on DevOps Journey by Brad Morgan. How do I keep...
RBAC management is crucial to securing a Kubernetes cluster and ensuring compliance with regulations and...
Security gaps in a Managed Kubernetes Environment - In this article, we examine the impact...

This post compares popular Kubernetes security and compliance frameworks, how they differ, when to use...

Discover the complex bond between AI and software development, as malicious actors exploit AI code...

Introduction Kubernetes has emerged as the de facto standard for container orchestration, enabling organizations to...

In this blog post, we will introduce the concept of relevancy of vulnerabilities to a...

Improve Kubernetes compliance with ARMO Platform's user-friendly Compliance Score for enhanced security. Click here to...

This post discusses the five Trust Services Criteria (TSC) of SOC 2 and how they...